Hi-Spider advertising number of URLs blocked:

I was able to get remote access on this device by uploading a perl script using the router's built-in network-attached storage feature. I wrote the perl script to immediately initiate a reverse shell upon execution. Since the router's web server was configured to execute any file ending in *.pl as a perl script, I was able to get a shell on the router by “downloading” the perl script that I had uploaded.
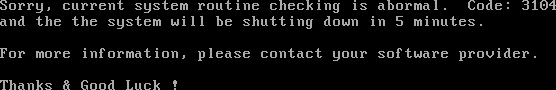
After a while, the Hi-Spider router would eventually detect that it had been hacked, requiring me to occassionally repeat the process:
Most notably, I found that the router software grossly exaggerated its censorship capabilities (see below).
Lists
From 2009:
- *.conf file advertising 70,601 blocked URLs, which is what is advertised in the Web UI
- URL blacklist containing only 601 blocked URLs (the router programmatically exaggerates the total count by 70,000 or by over 11,647%)
- Singleton keyword blacklist
From 2011:
- *.conf file advertising 71,225 blocked URLs, which is what is advertised in the Web UI
- URL blacklist containing only 1,225 blocked URLs (the router programmatically exaggerates the total count by 70,000 or by over 5,714%)
- (No keyword blacklist)
This material is based upon work supported by the National Science
Foundation under Grant No. 0844880. Any opinions, findings, and
conclusions or recommendations expressed in this material are those of
the author(s) and do not necessarily reflect the views of the National
Science Foundation.
![]()